Why Moz Ranking Is A Tactic Not A strategy
페이지 정보

본문
 The top of the stack is calculated by including the value at offset 0x28 to the address at the top of the VM’s state struct. We beforehand saw that earlier than running the VM, the program allocates 0x1002c bytes of space and units offset 0x28 to 0x10000. The VM’s state is 0x2c bytes, and the remaining space is the digital stack. As we decided from static analysis the VM stores its state starting at ebx, and has a register for every of the general purpose registers, from offset 0x4 to 0x20. It also has a customized register at offset 0x0 which appeared only for use for intermediate operations. However it appeared as if it would always end in an error, and it was never used within the bytecode so I couldn’t examine it any further and selected to symbolize it with a ud2 instruction. It performs a bitwise and with the register and 0x800, and if the result's non-zero then it strikes our place within the bytecode (i.e. the instruction pointer). The last slot within the context, at offset 0x28, is a form of stack pointer.
The top of the stack is calculated by including the value at offset 0x28 to the address at the top of the VM’s state struct. We beforehand saw that earlier than running the VM, the program allocates 0x1002c bytes of space and units offset 0x28 to 0x10000. The VM’s state is 0x2c bytes, and the remaining space is the digital stack. As we decided from static analysis the VM stores its state starting at ebx, and has a register for every of the general purpose registers, from offset 0x4 to 0x20. It also has a customized register at offset 0x0 which appeared only for use for intermediate operations. However it appeared as if it would always end in an error, and it was never used within the bytecode so I couldn’t examine it any further and selected to symbolize it with a ud2 instruction. It performs a bitwise and with the register and 0x800, and if the result's non-zero then it strikes our place within the bytecode (i.e. the instruction pointer). The last slot within the context, at offset 0x28, is a form of stack pointer.

I may inform the VM was more than likely stack based mostly, and appeared to have a number of different addressing modes, nevertheless it was straightforward to waste time tracing the precise execution of every handler. Using an anti-anti-debug plugin reminiscent of ScyllaHide would have been the simplest answer, nonetheless I needed to grasp every anti-debug check before evading it. Evading these checks is pretty simple: I merely patched the beginning of every perform to leap to the ret instruction at the tip. Later capabilities will pop this address off the stack and jump to it. 404440 demonstrates how the handlers push the address of a function to be executed later to the stack, and jump to the subsequent operate. I added a breakpoint at the principle perform we recognized before, and let this system execute, however I ran into an issue: the main function is never reached. When we load the binary in x32dbg the initial breakpoint is where ntdll.dll hundreds the application. Let’s attempt to debug the binary with x32dbg.
Moreover, attempt to use synonyms and related key phrases, as they’ll make your textual content simpler to know and may even improve Seo. If we check the console we can see that you just discover a bizarre sound coming out of the device, so you throw it away in concern! Remember, in one of the case studies the enterprise spent six months constructing up content material before they even thought of reaching out to different purchasers. Find out dozens of engaging and a focus-grabbing content material concepts that your ideal customers would love to learn. Captioning is turning the audio content of a video into textual content and displaying it on a display or monitor. Backlinks help establish that your webpage and its content material are precious to users. Instead this system enters some TLS callback capabilities (that are functions a program can register to execute earlier than the principle program) and eventually termintates. My implementation will be found here.
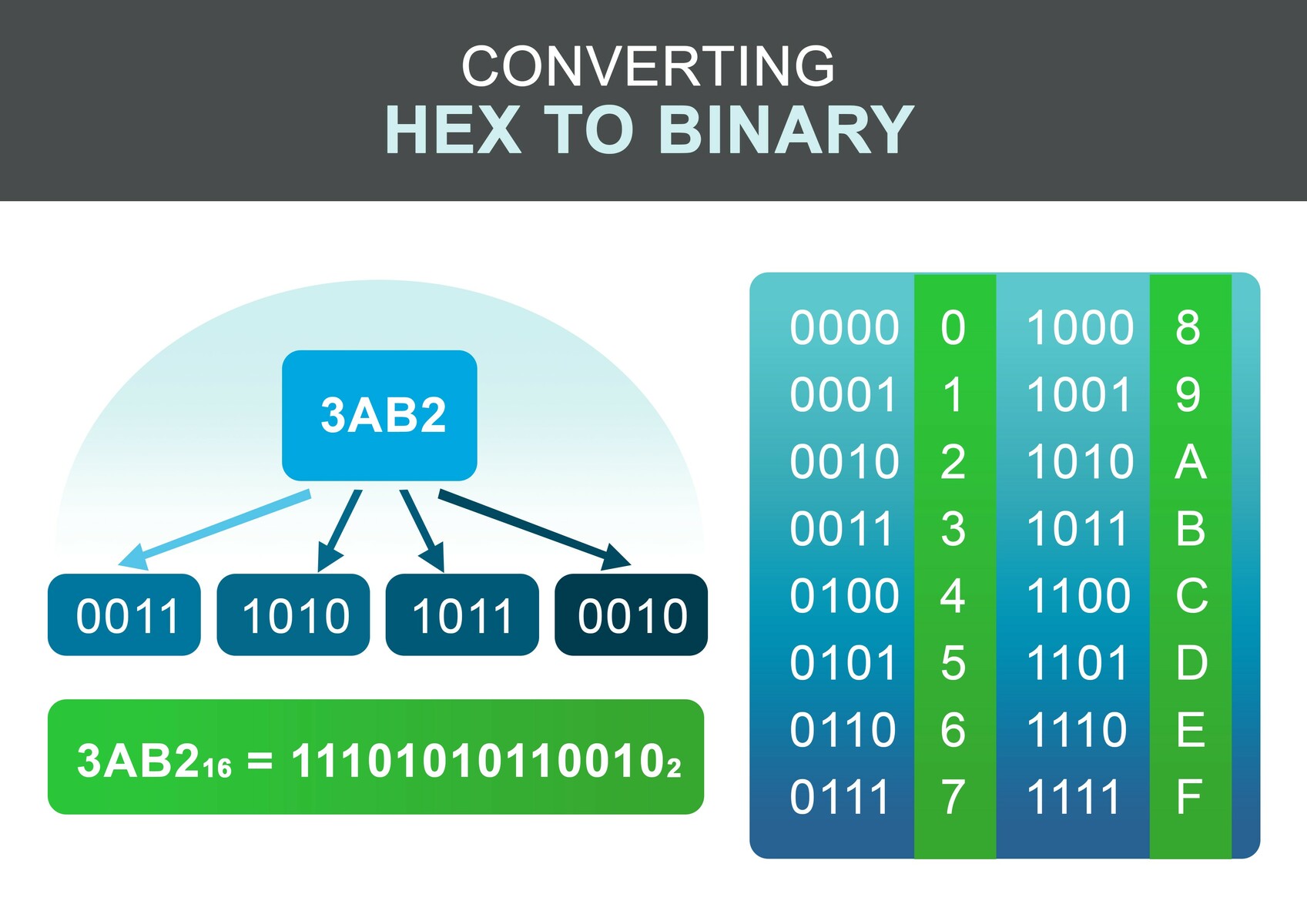
If you are you looking for more information regarding how to convert hex to binary visit our web site.
- 이전글5 Killer Quora Answers To Natural Gas Patio Heater 25.02.15
- 다음글Three Incredibly Useful Domain Authority Check For Small Businesses 25.02.15
댓글목록
등록된 댓글이 없습니다.